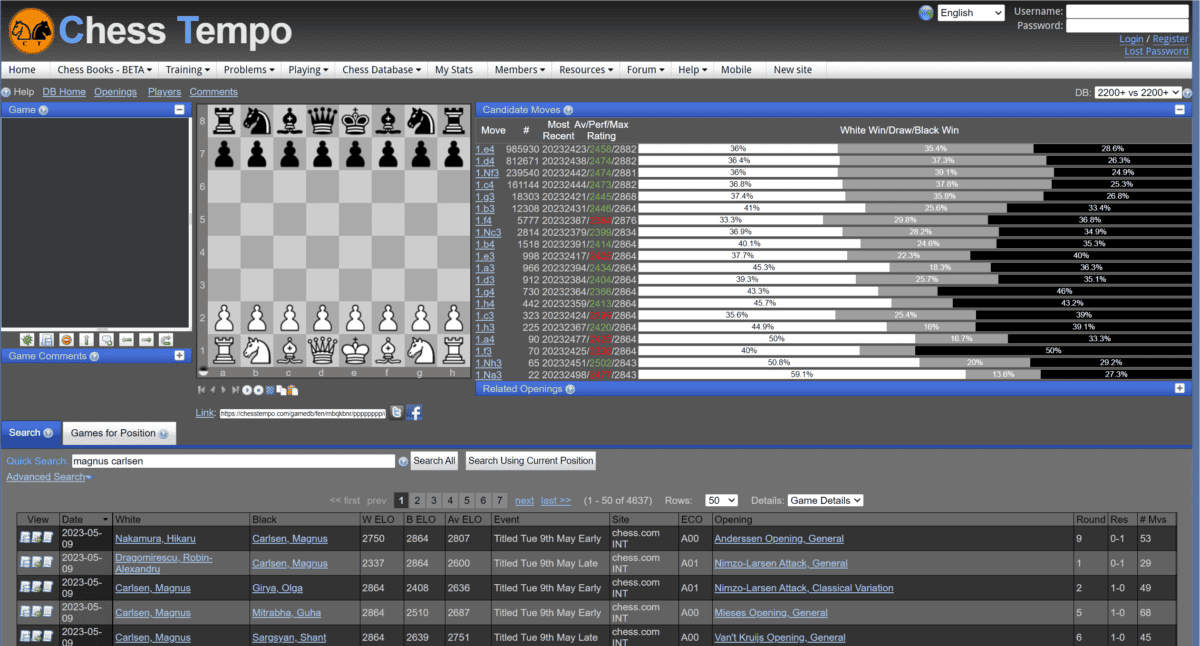
Exploit opening inaccuracies by finding a good plan
Por um escritor misterioso
Last updated 20 setembro 2024
Do your best to understand the implications of your moves. This will take you a long way towards mastery.

Exploiting Typical Opening Errors - Chess Lessons
What is a vulnerability disclosure and why is it important?

All the Shah's Men: An American Coup and by Kinzer, Stephen

What Is a Security Vulnerability? Definition, Types, and Best Practices for Prevention - Spiceworks
Fake News, Lies, and Other Familiar Problems
:max_bytes(150000):strip_icc()/tragedy-of-the-commons-c807f6c516ca4a729896ab5e8b17154f.jpg)
What Is the Tragedy of the Commons in Economics?
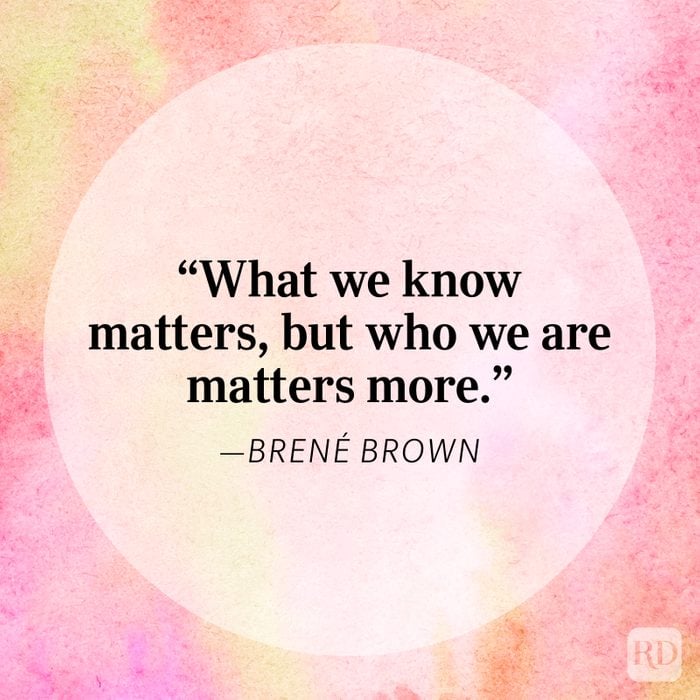
50 Brené Brown Quotes on Vulnerability, Courage, and Motivation for 2023

OpenSSF details top 10 secure software development principles - SDxCentral
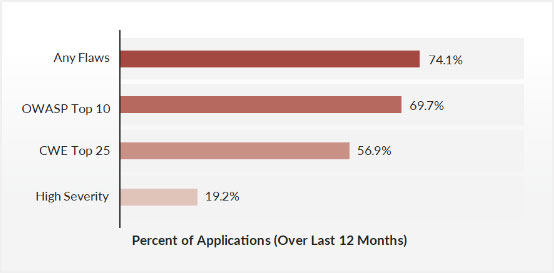
OWASP Top 10 Vulnerabilities
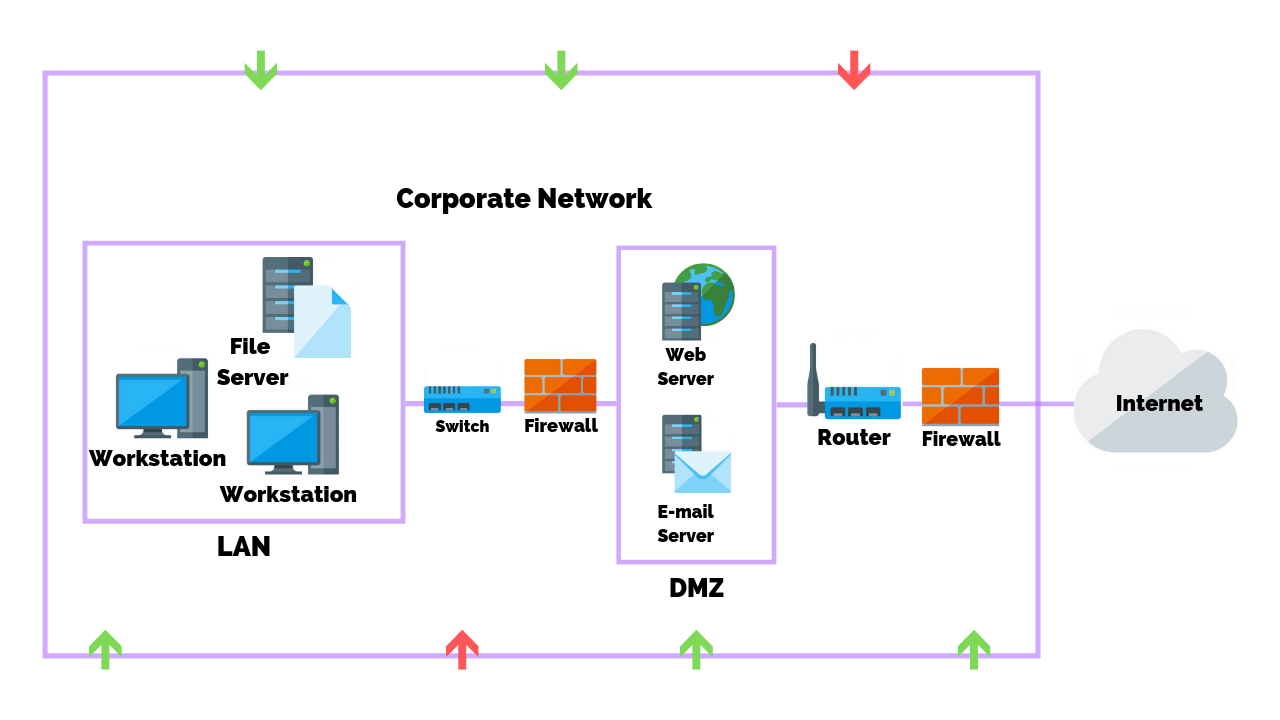
Common Types Of Network Security Vulnerabilities
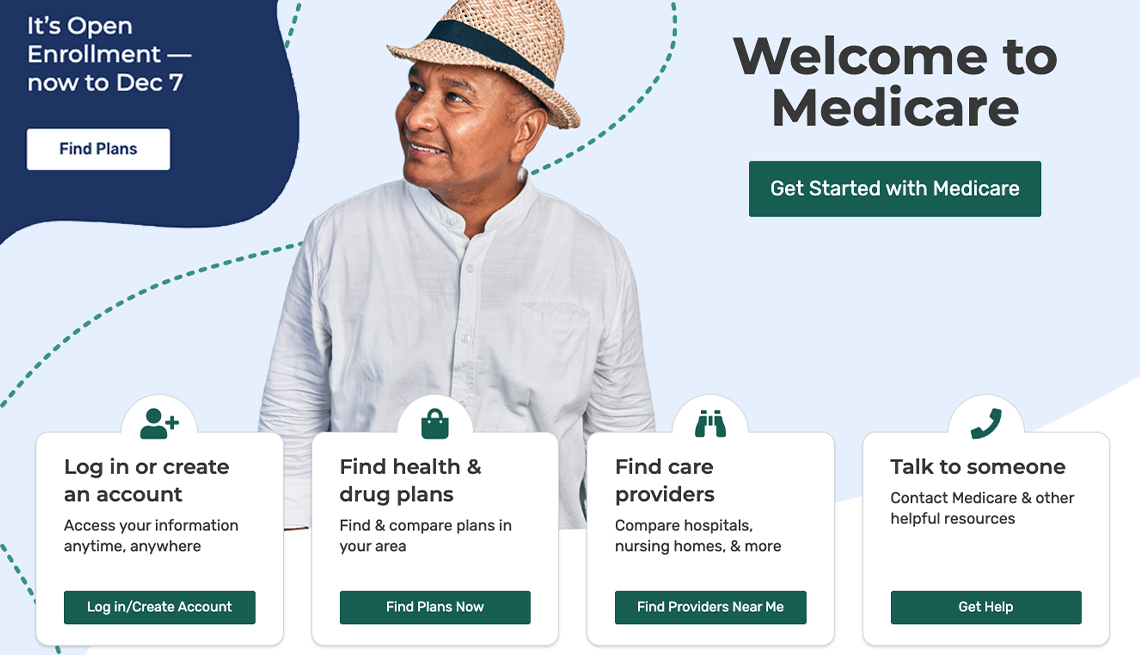
Medicare Open Enrollment: What You Need to Know Now

Target Weaknesses to Exploit Opening Inaccuracies

Bitdefender Review 2023: How Good is this Antivirus?

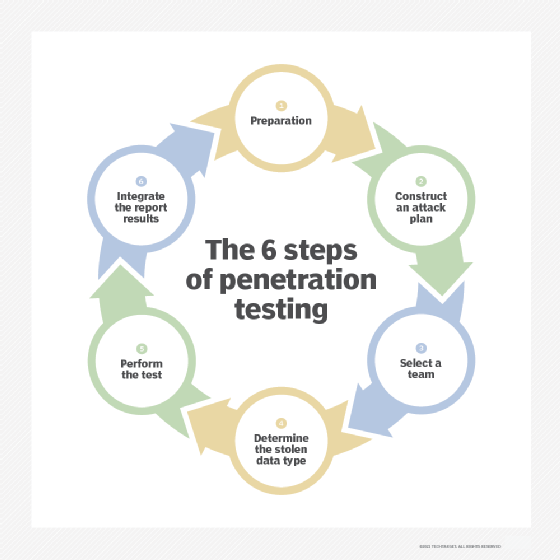
EC-Council - Penetration testing is the process of identifying the security vulnerabilities in a system or network and trying to exploit them. As with any activity, people make some common mistakes when
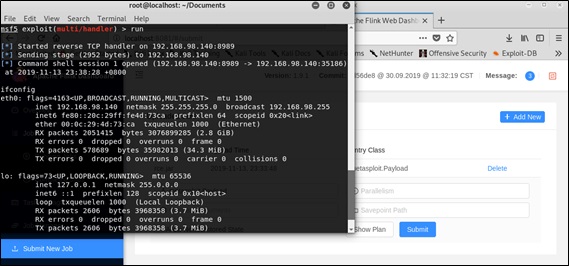
Apache Flink Arbitrary Jar Package Upload Threat Alert - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.
Recomendado para você
você pode gostar













:strip_icc()/i.s3.glbimg.com/v1/AUTH_59edd422c0c84a879bd37670ae4f538a/internal_photos/bs/2022/q/k/PQGZHlShiHilU68cBL7Q/whatsapp-image-2022-12-21-at-19.45.54.jpeg)