Malware analysis Malicious activity
Por um escritor misterioso
Last updated 20 setembro 2024
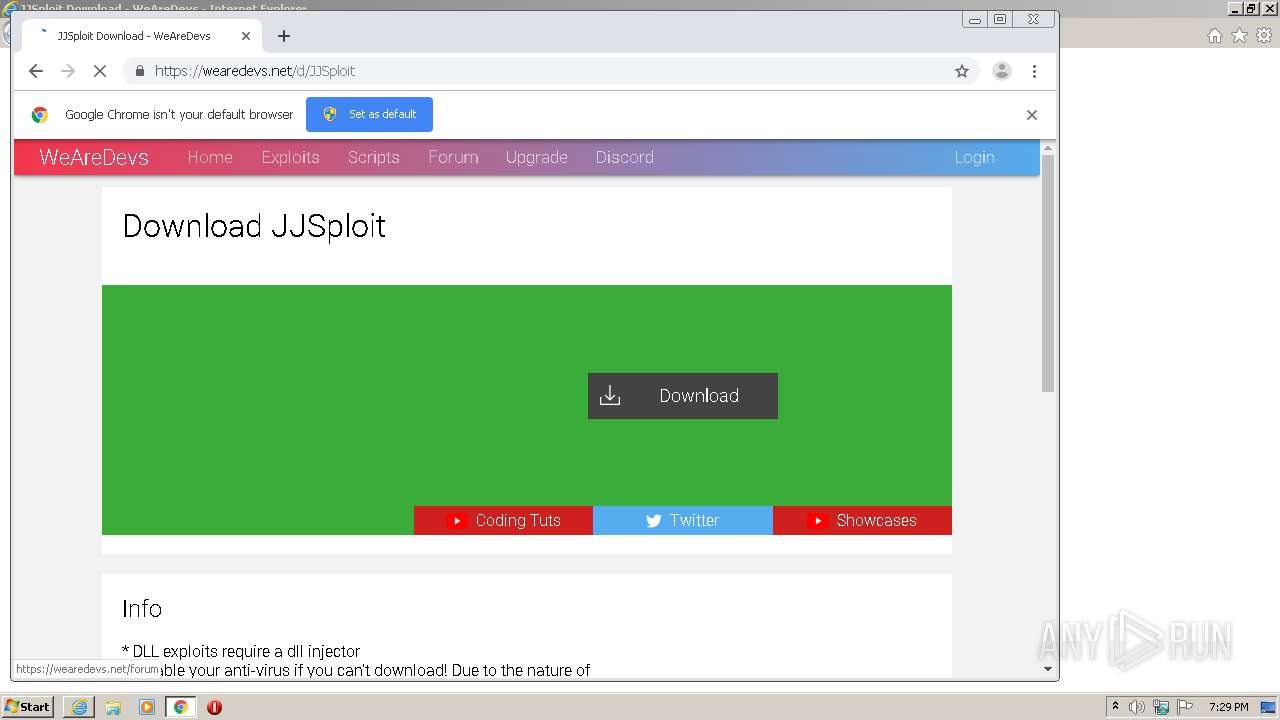

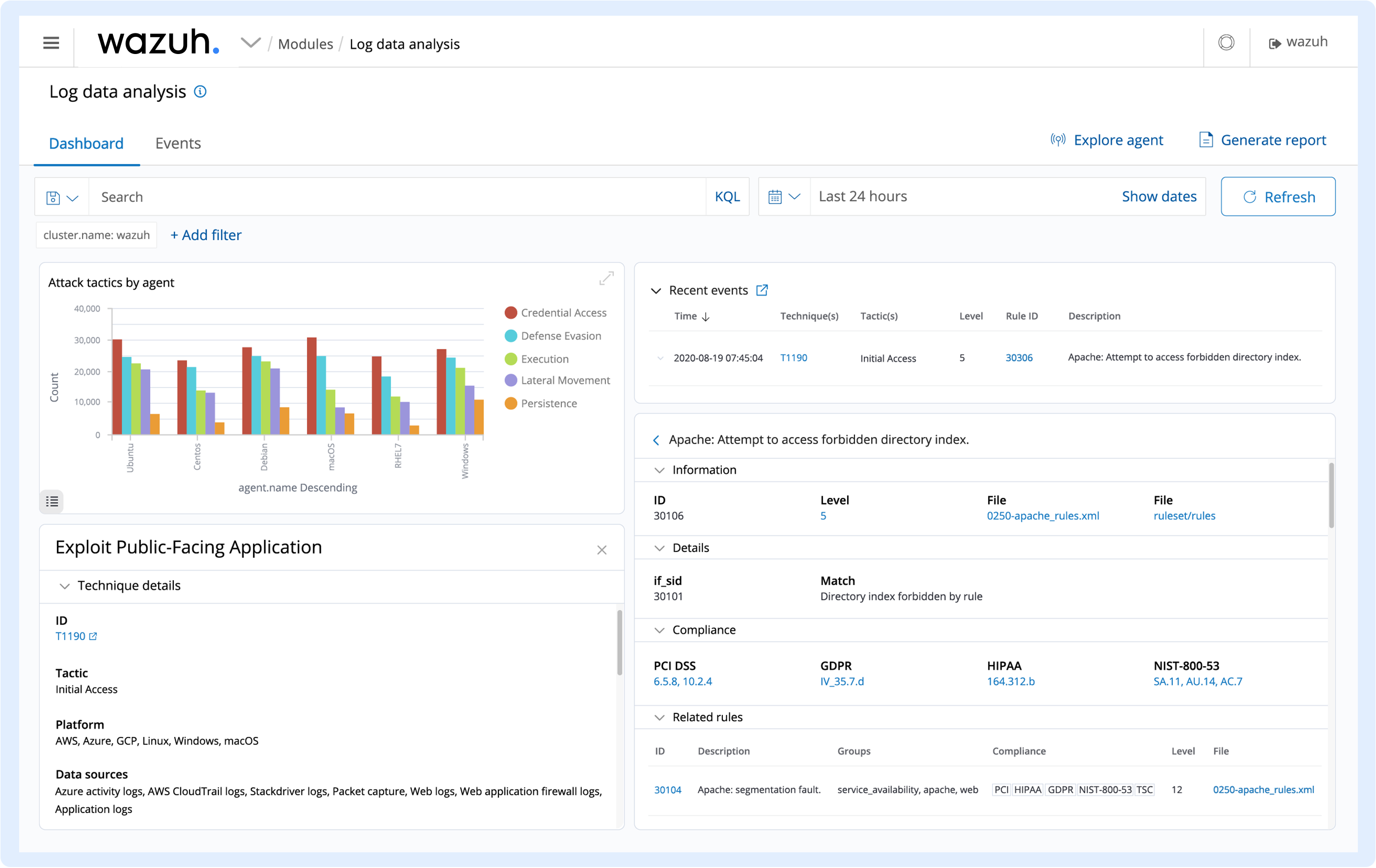
Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

MetaDefender Cloud Advanced threat prevention and detection

AI and Automation - DZone

Malware analysis AIO_4.9.8__ed.rar Malicious activity

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

Feature Extraction and Detection of Malwares Using Machine Learning

Dynamic malware analysis [34]
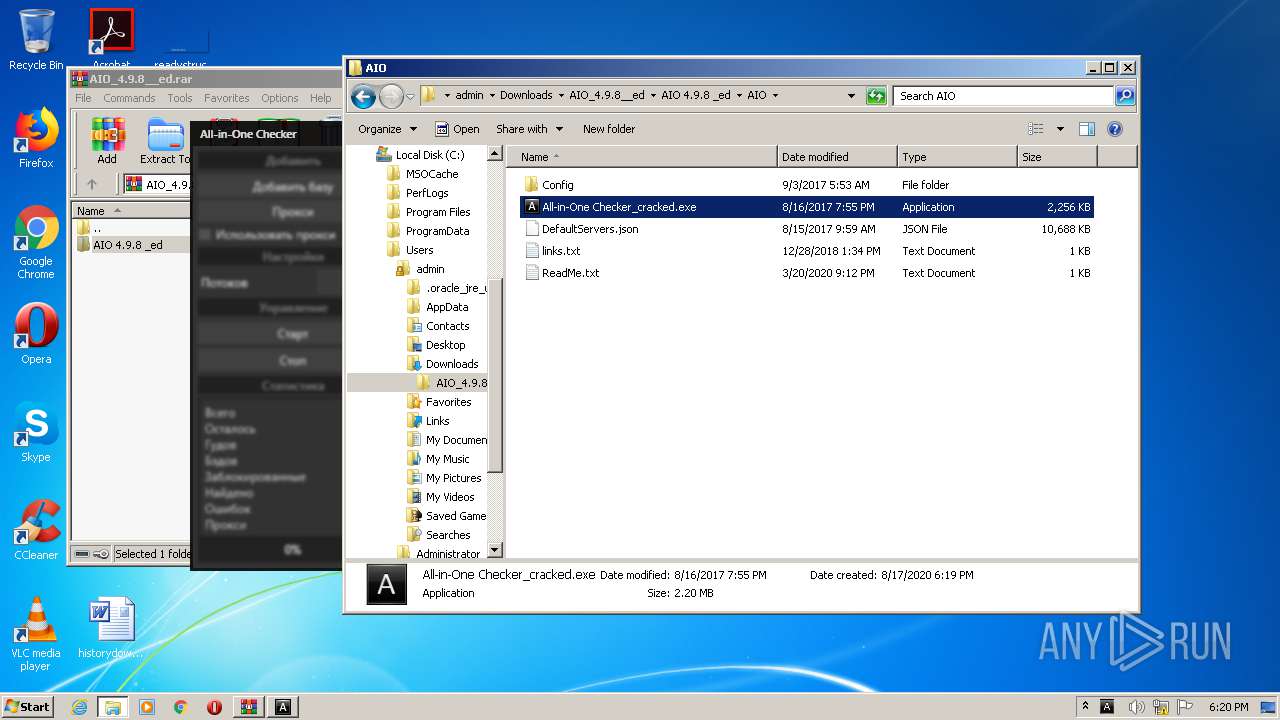
Malware analysis AIO_4.9.8__ed.rar Malicious activity
How to Analyze Malware's Network Traffic in A Sandbox

Malware analysis CQChallenge5.zip Malicious activity
Overview

Playbook for Malware outbreak

Malware Analysis: Steps & Examples - CrowdStrike

Malware analysis Program_Install_and_Uninstall Malicious activity
Recomendado para você
você pode gostar






![A Grande Batalha dos Deuses] Perfil dos Guerreiros Deuses (Filme) Cavaleiros do zodiaco anime, Cavaleiros do zodiaco, Cavaleiros do zodiaco seiya](https://i.pinimg.com/originals/33/3e/3f/333e3f8db0c558c8deb6cb9ad76a7719.jpg)
/i.s3.glbimg.com/v1/AUTH_59edd422c0c84a879bd37670ae4f538a/internal_photos/bs/2023/b/Y/1TjgX4SyAtq0k20qbBXA/cavalo.jpg)