Malware analysis Malicious activity
Por um escritor misterioso
Last updated 10 novembro 2024


How to Do Malware Analysis?

How to Analyze Malware's Network Traffic in A Sandbox

Malware analysis mykey_.rar Malicious activity

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Malware analysis cd53fba6ddd4ae4ef7a5747c6003236c85791477854cc1b7ce00e0f8ee7677d9 Malicious activity

Malware analysis index.html Malicious activity

How to build a malware analysis sandbox with Elastic Security

Malware Analysis: Steps & Examples - CrowdStrike
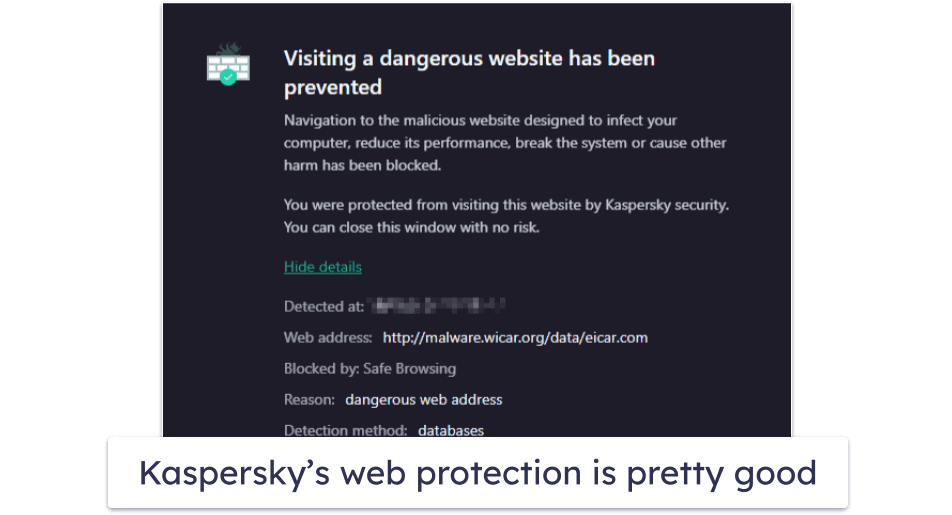
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

AlienVault - Open Threat Exchange
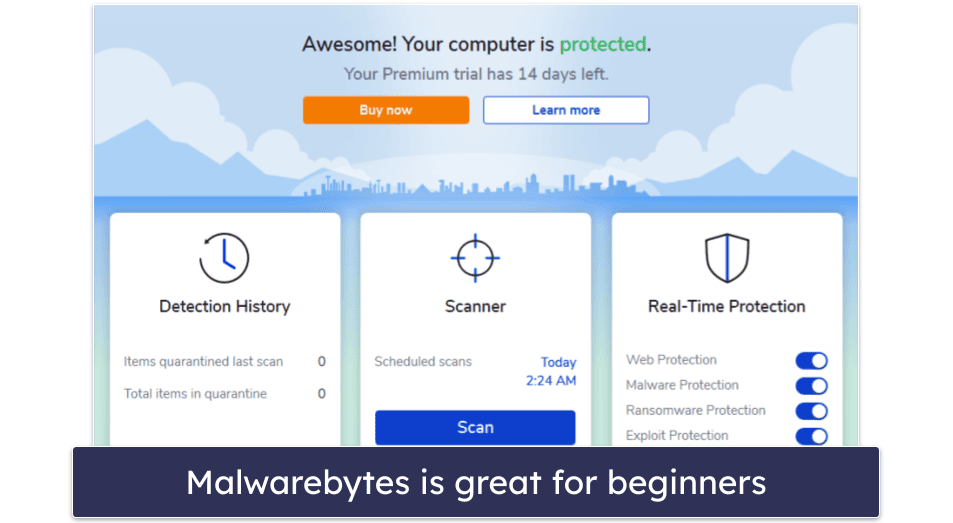
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

AI and Automation - DZone

Malware analysis lockysample.bin.zip Malicious activity

Cybersecurity Search Engine
Recomendado para você
você pode gostar













![Made a minimalistic wallpaper for Developers / Programmers [1920x1080] : wallpaper](https://i.pinimg.com/736x/ee/70/0c/ee700cf9a8a814ad0995772a1b1d18da.jpg)
