Malware analysis Malicious activity
Por um escritor misterioso
Last updated 23 setembro 2024

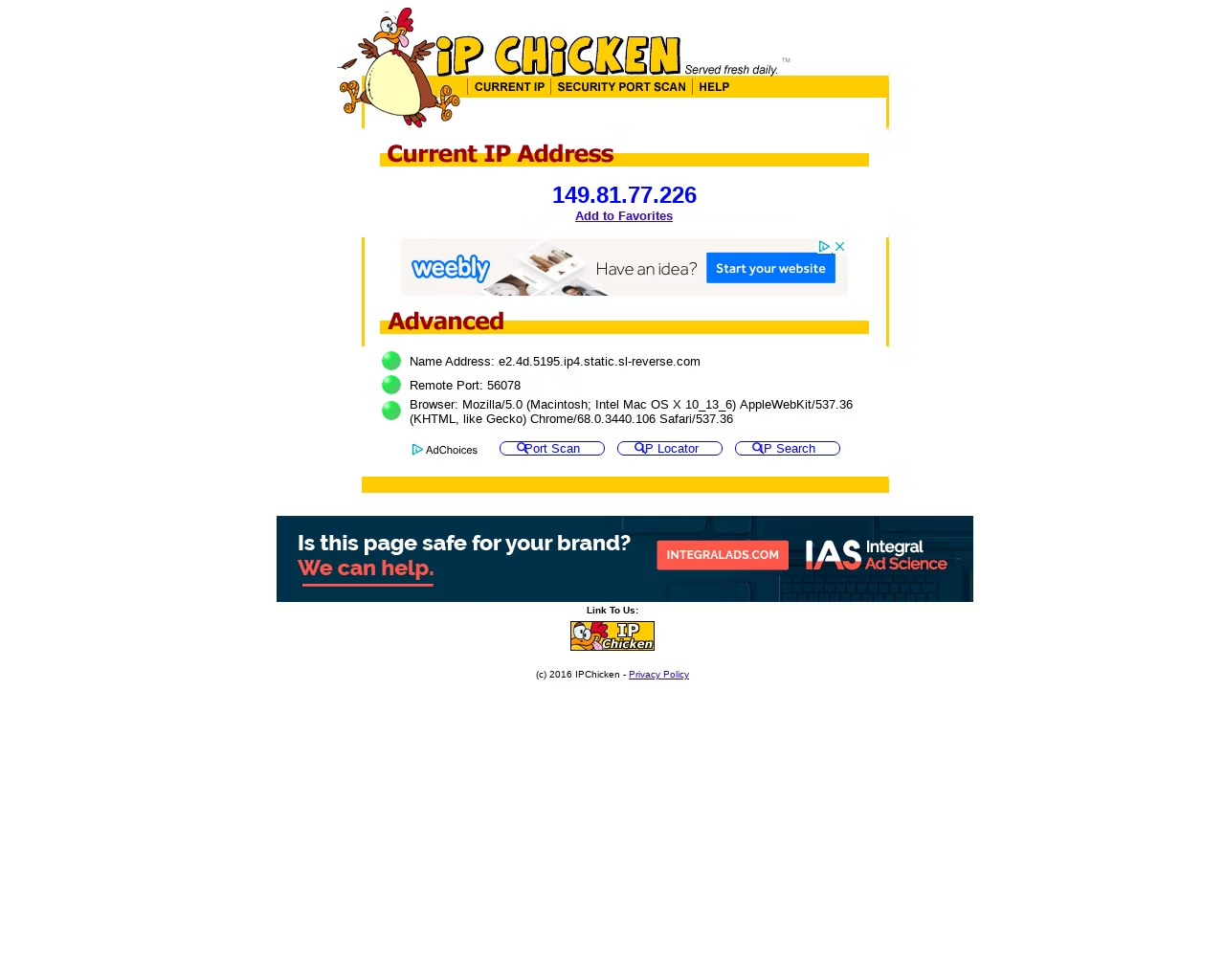
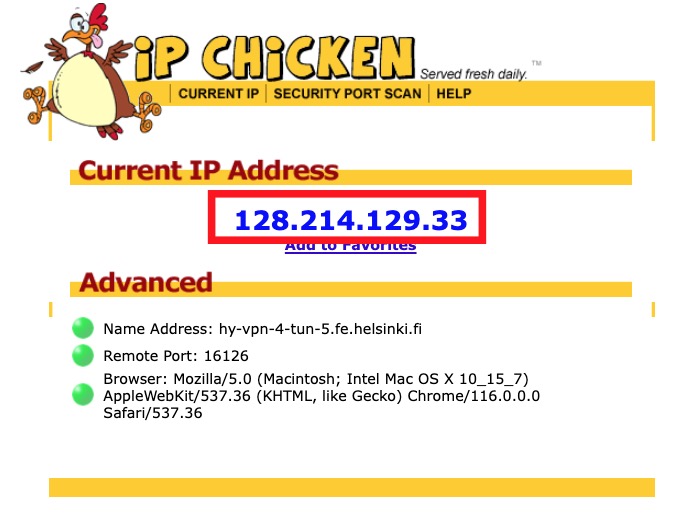
Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

What is Malware? Definition, Types, Prevention - TechTarget

Malware analysis tt.7z Malicious activity
Malware analysis Malicious activity

Malware analysis index.html Malicious activity

Endpoint Detection and Response, Free - What is EDR Security?

Advanced Automated Malware Analysis – Kaspersky Research Sandbox

Playbook for Malware outbreak
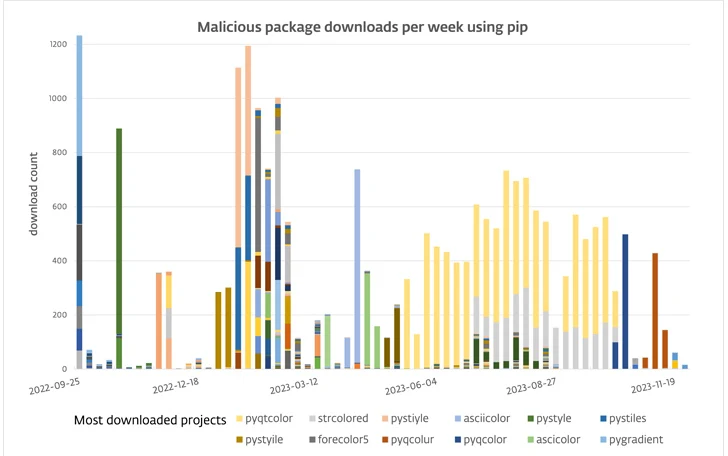
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

Info stealers and how to protect against them

Malware analysis AIO_4.9.8__ed.rar Malicious activity
Recomendado para você
você pode gostar
:max_bytes(150000):strip_icc()/B3-FindYourIPAddressinWindows-annotated-700617f96c9749f9935623e6a1c41f00.jpg)