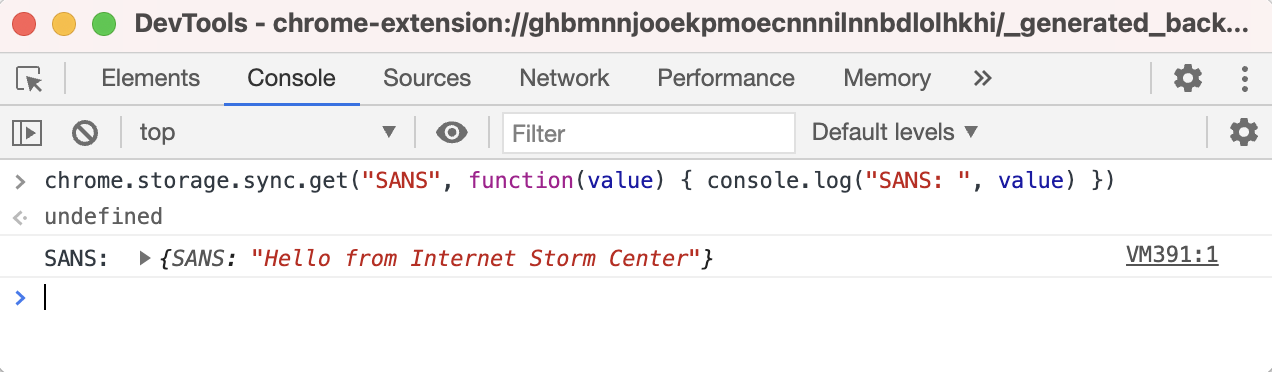
Abusing Google Chrome extension syncing for data exfiltration and C&C - SANS Internet Storm Center
Por um escritor misterioso
Last updated 20 setembro 2024
JhoneRAT: Cloud based python RAT targeting Middle Eastern co - vulnerability database

Free Automated Malware Analysis Service - powered by Falcon Sandbox - Viewing online file analysis results for 'RealPlayer.exe
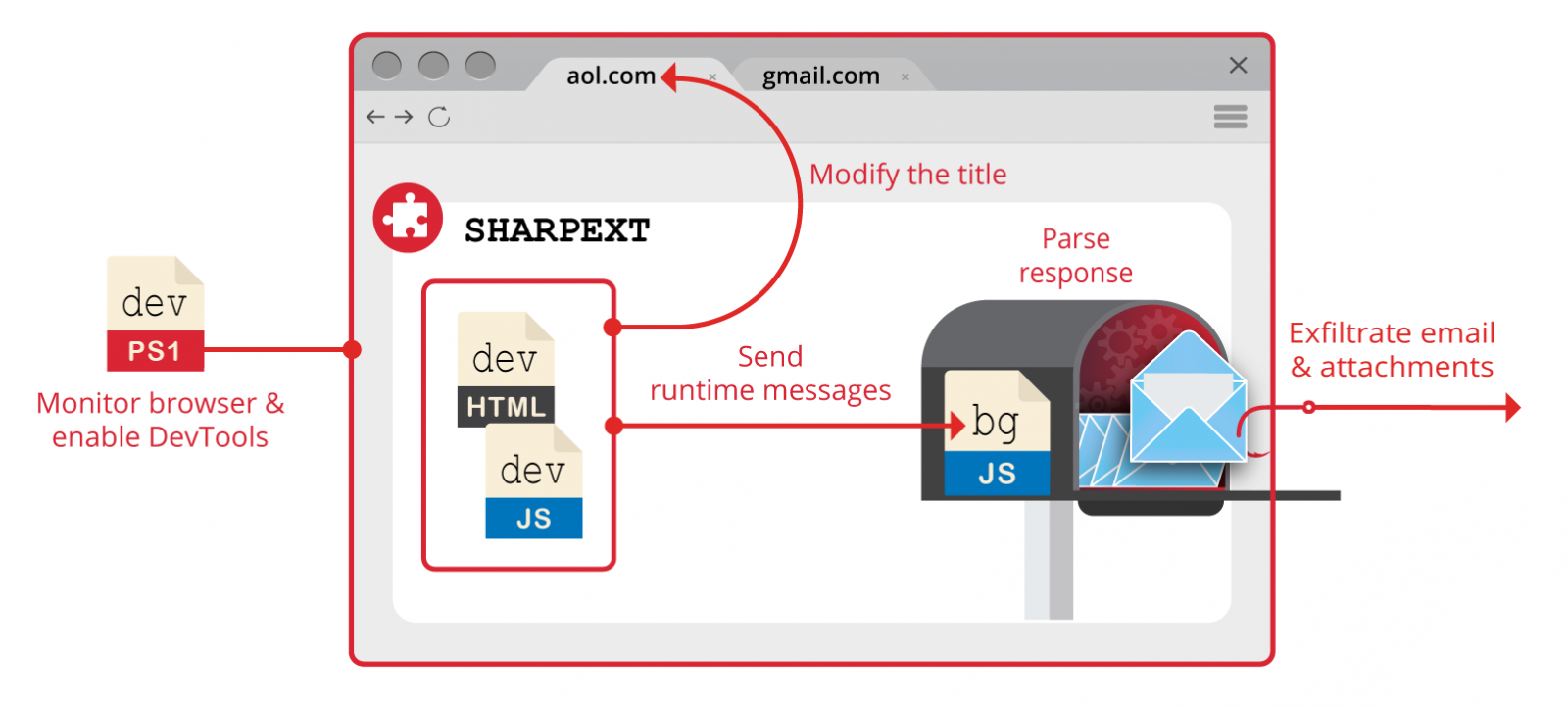
Cyberspies use Google Chrome extension to steal emails undetected
Security-News/Twitter/Zube/2016/2016_04_30.txt at master · trietptm/Security-News · GitHub

PDF) Detecting Covid-19 Chaos Driven Phishing/Malicious URL Attacks by a Fuzzy Logic and Data Mining based Intelligence System
awesome-reverse-engineering/Readme_full_en.md at master · 6700github/awesome-reverse-engineering · GitHub

Chrome Sync can be misused for malware distribution – Born's Tech and Windows World

Detecting Covid-19 chaos driven phishing/malicious URL attacks by a fuzzy logic and data mining based intelligence system - ScienceDirect

Detecting Covid-19 chaos driven phishing/malicious URL attacks by a fuzzy logic and data mining based intelligence system - ScienceDirect

New macro-less technique to distribute malware - vulnerability database

OSINTer - Article List
Encl Cyber Warfare, PDF, Computer Virus
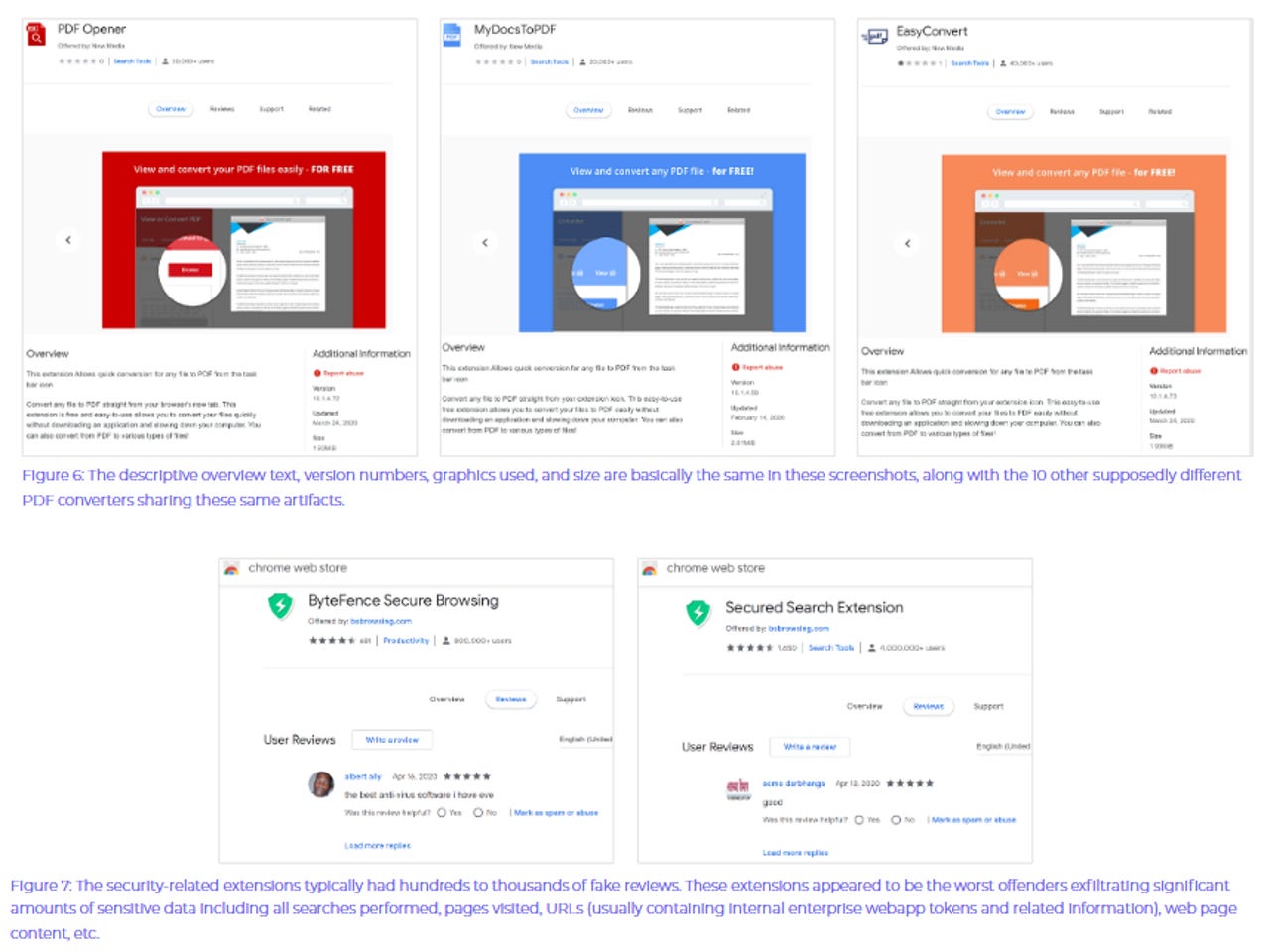
Google removes 106 Chrome extensions for collecting sensitive user data
Recomendado para você
você pode gostar